- cross-posted to:
- privacy@lemmy.ml
- cross-posted to:
- privacy@lemmy.ml
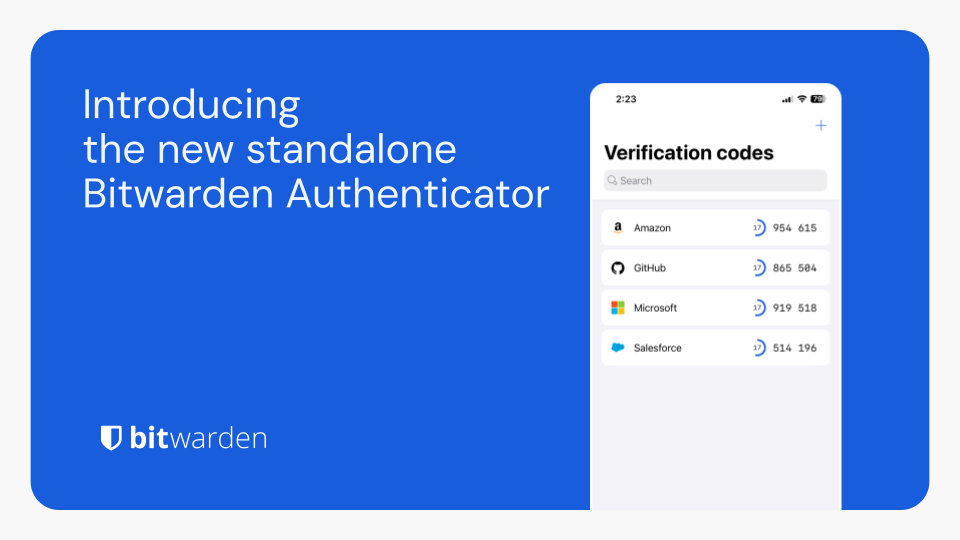
Bitwarden Authenticator is a standalone app that is available for everyone, even non-Bitwarden customers.
In its current release, Bitwarden Authenticator generates time-based one-time passwords (TOTP) for users who want to add an extra layer of 2FA security to their logins.
There is a comprehensive roadmap planned with additional functionality.
Available for iOS and Android


Is there a good reason I don’t know about to prefer this over Aegis?
No, they’re both ostensibly open source and standalone. I’m an avid Bitwarden Free user, but Aegis has been my go-to for a long time.
If it’s a standalone completely offline app, like Aegis, I’m at a loss to what they could offer that is any different than what Aegis already offers.
If you look at the roadmap they have in the blogpost, they are apparently planning tighter integration with the existing bitwarden suite
…but wouldn’t that undermine the fact that it’s standalone and offline?
The idea is that it can then work both says, like https://ente.io/auth does
Sand the fact that it’s a 2fa. A thicker integration with bitwarden would make it like a 1.5fa
I don’t see why it would if it’s optional
How so? They already have TOTP built-in to the app if you pay for premium, so this is just a free competitor to their own offering.
I’m guessing they’re trying to make it a “gateway” to getting people on Bitwarden. Start with the TOTP app, then use the password manager, then pay for premium. Or something like that.
2FA push is on the roadmap. Does aegis have that? Or am I just too dense to realise it does?
I mean, Aegis is 2FA? That’s literally all it is? It generates One Time Pad codes for various sites and apps that support authentication apps.
So, I’m not sure what you mean?
I’m not positive but I’m assuming they’re referring to a kind of MFA where the authenticating service pushes to the client you possess rather than relying on a temporal cryptographic key. I’ve got a few services which work that way
That’s indeed what I meant. Similar to how OKTA, battle.net, or the Microsoft authenticator works( in corporate environments).
You receive a push notification which asks if you’re trying to log in and approve it, followed by a fingerprint or a pin code to confirm, rather than having to type in the code generated by your app
Reading these comments, it feels like Aegis became the standard without me noticing.
Reading these comments I feel like I’m completely out of the loop because I’ve never even heard of Aegis
It doesn’t get a whole lot of attention but it’s the most mature open source authenticator app and one of the first ones you would find in fdroid. With that said, there’s nothing really standout about it or its features, it just works.
same
Just on Lemmy
interesting. what makes it special? i’m assuming it’s just like any other TOTP client?
Someone answered this for me. It’s just that it’s open source. If that matters to you, there you go.
I used to use Aegis, but after setting up my own vaultwarden, I use the normal bitwarden app/plugin on all my systems for passwords and TOTP.
The advantages are that I don’t need my phone to login, the keys are synced and backuped in the encrypted vaultwarden database, which I can then handle with normal server backup tools. It still works offline, because bitwarden app caches the password.
This is IMO much more convenient and secure (in a way that loosing access to a device doesn’t shut you out, and you don’t need to trust third parties) then most other solutions.
Even if I hosted my own BitWarden vault, I wouldn’t put my passwords and 2 factor tokens in the same place because it’s eliminating the benefits that 2 factor provides if someone somehow manages to get into my vault.
2 factor came into our life because people were using same passwords everywhere. With unique passwords, which are easy with password managers, it’s rarely needed.
That may have been part of the reason, but the theory behind MFA is that there are 3 primary ways to authenticate who you are: what you know (password), what you have (secure one time password generator or hardware token), and what you are (biometrics). Password managers and digital one time password generators have kind of blurred the lines between passwords and one time passwords, but you’re raising your risk a bit if you put them in the same place.
With unique passwords, the attack surface just changes. Instead of attacking the passwords, attackers attack the password managers. LastPass, Okta, and Passwordstate each had breaches, and the first two are quite popular.
That doesn’t mean Bitwarden is at risk (not sure if it has been targeted), it just means that attackers are finding success going after password managers, so they could go after Bitwarden. Maybe they’ll sneak in an xz-style bug that’ll allow attackers to steal credentials en-route, idk.
So it’s a matter of good/better/best:
The overhead from using a separate 2FA app is pretty low, just make sure it encrypts your keys and you trust it (FOSS is a good indicator of trust).
There is not much difference between having two apps (password manager and authenticator app) or one app, that does both on the same device.
So, if you want more security, then you have to deal with a hardware token and never with a authenticator app. But then if you loose your token, then you have trouble.
I don’t think it caches the password. Rather a decryption key is derived from your password and is used to unlock the encrypted blob.
What I meant is that is caches the password database for offline use.
For now: No.