- cross-posted to:
- technology@lemmy.world
- cross-posted to:
- technology@lemmy.world
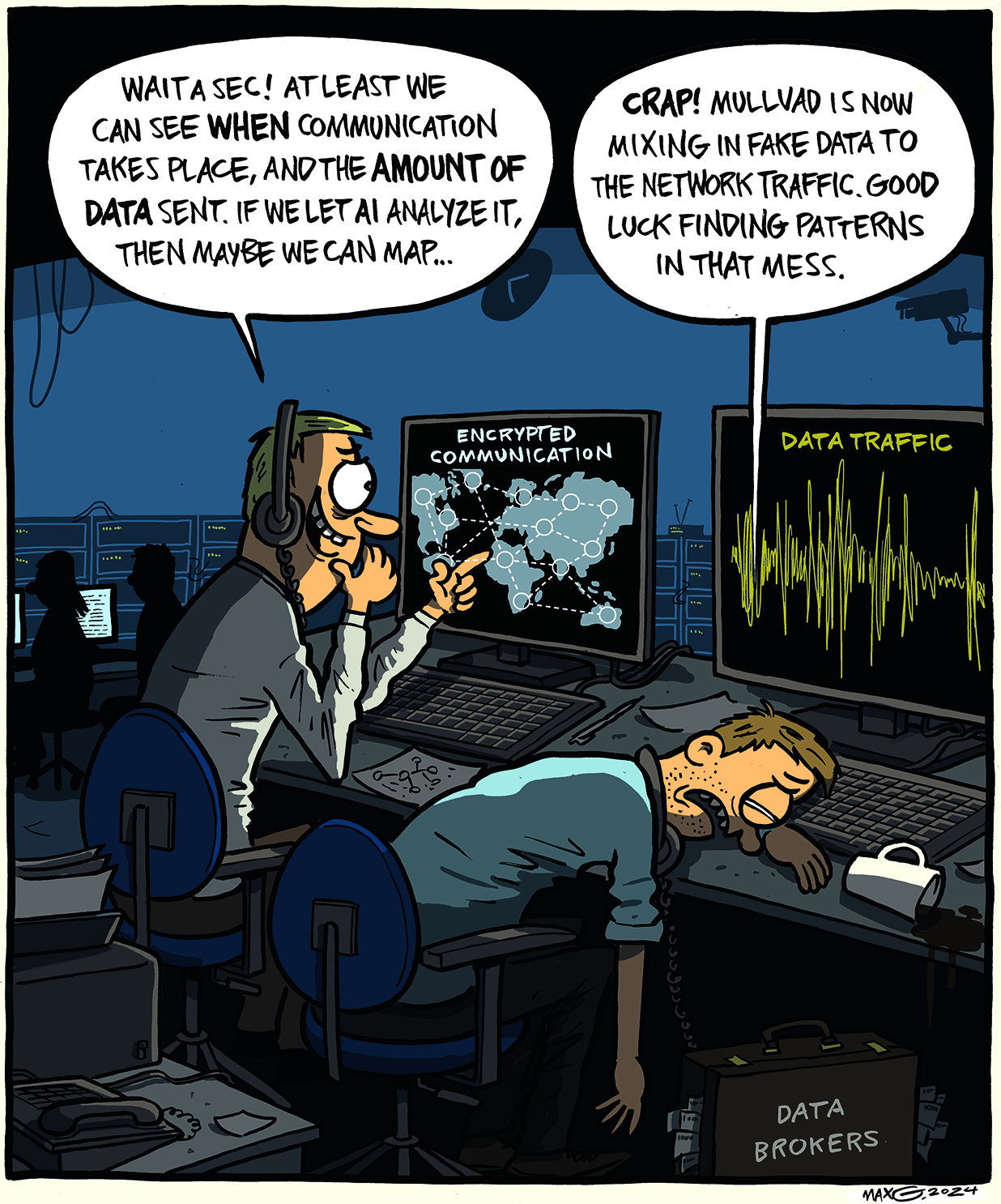
Even if you have encrypted your traffic with a VPN (or the Tor Network), advanced traffic analysis is a growing threat against your privacy. Therefore, we now introduce DAITA.
Through constant packet sizes, random background traffic and data pattern distortion we are taking the first step in our battle against sophisticated traffic analysis.


Thanks very much, I believe I understand that part now, like a fingerprint to associate to site components like pulled in js, css, etc. I still don’t understand, though, how they associate that to a particular user of a VPN. Does each request done through a VPN include some sort of identifier for each of us or is AI also doing something to put these requests in a particular user’s bucket?
I think it was more targeting the client ISP side, than the VPN provider side. So something like having your ISP monitor your connection (voluntarily or forced to with a warrant/law) and report if your connection activity matches that of someone accessing a certain site that your local government might not like for example. In that scenario they would be able to isolate it to at least individual customer accounts of an ISP, which usually know who you are or where to find you in order to provide service. I may be misunderstanding it though.
Edit: On second reading, it looks like they might just be able to buy that info directly from monitoring companies and get much of what they need to do correlation at various points along a VPN-protected connection’s route. The Mullvad post has links to Vice articles describing the data that is being purchased by governments.